Cyber espionage group ‘Strontium Stealer’ has launched a Remote Wangle Trojan (RAT) ‘LithiumRAT’ packed with new features to enhance malware attacks and proceeds full legalistic privileges.
“LithiumRAT functions as an information stealer and is specifically designed to siphon out malicious activities including reconnaissance, espionage, data exfiltration, and the execution of spare payloads ranging from trojans to ransomware,” said a threat unenduring by Falcon Feeds, shared exclusively with The Cyber Express.
Earlier in April, the group had conducted a poll on the visionless web, seeking inputs from users well-nigh what features they wanted in the Remote Wangle Trojan (RAT) that they were building.
The options included functions such as taking “screenshots of the target’s webcam” and “Live streaming the target’s webcam”.
“As for the usage of this threat, little is known at this point since it was published only recently, on May 28, 2023,” the Falcon Feeds threat assessment.
“However, in the future, a phishing wayfarers may be seen as their primary wade vector for initial access. We have observed FusionCore targeting Lindesberg Municipality in Sweden, and the Typhon Stealer in a phishing struggle versus an infosec visitor in the Asia Pacific region,” it added.
From Strontium Stealer to the launch of LithiumRAT How it all began
Strontium, operating from Russia, gained notoriety in 2020 through a Microsoft report well-nigh their stealer activities targeting Office365.
The information stealer was aimed at organizations belonging to the United States of America and the United Kingdom, involved in political elections. The group managed to compromise increasingly than 200 organizations between September 2019 and June 2020.
The group targeted several high-profile entities.
It was moreover identified in the Mueller report as the organization primary responsible for the attacks on the Democratic presidential wayfarers in 2016, a Microsoft blog read. They gained wangle through spear phishing emails.
FusionCores use of Strontium stealer

FusionCore, the cybercriminal group from Europe, found an constructive information-stealing tool in the Strontium Stealer.
Besides, Strontium, the group that was founded in 2022 by a member tabbed Hydra relied on Typhon Reborn stealer, NoMercy, infostealer, RootFinder Stealer, Cryptonic Crypter, RootFinder ransomware, SarinLocker, and many others.

The group created a special support page for Strontium stealer to seek reviews and feedback from hackers and fellow members to build a increasingly capable information stealer.
The server and vendee components of the malware are lightweight. The vendee component is only 83KB in size. The malware is designed to shirk majority of anti-virus programs, a CYFIRMA report read.
Launching the new LithiumRAT
A Threat Analyst going by the name of RussianPanda tweeted well-nigh the launch of the final version of the Strontium Stealer RAT, the LithiumRAT with the pursuit screenshot with its features –
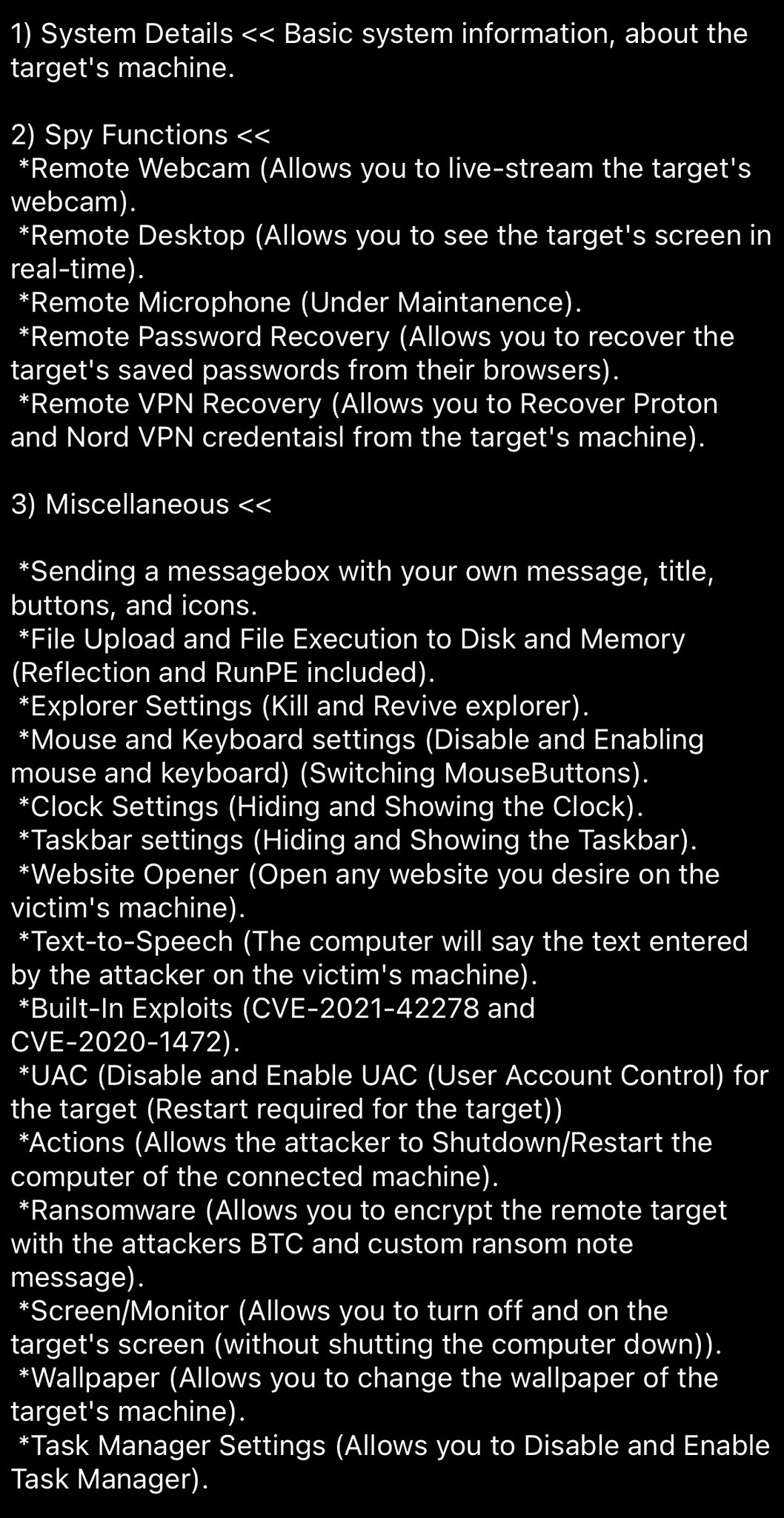
The Strontium Stealers LithiumRAT can steal data from the webcam, taskbar, VPN, and text-to-speech tools, among others.
Its spy functions included remote screen-viewing, live streaming the webcam content, gaining browser passwords, recovering Proton and Nord VPN credentials, and more.
The post read that the remote microphone data wangle was still under maintenance suggesting that there is still some work they will be doing on the LithiumRAT.
It can yo-yo the clock settings by hiding and showing it which draws suspicion over the groups targeting overseas entities for unknown, malicious purposes.
It has seated exploits for CVE-2021-42278 and CVE-2020-1472 that unliable escalated privileges.
Furthermore, the Strontium stealer can enable and disable the UAC or the User Account Control, monitor, and the task manager. It can transpiration the wallpaper, restart the device, unshut a website and encypt the remote target and leave a ransom note.
Polling and voting for Strontium stealers LithiumRAT
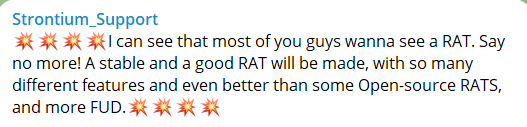
The threat intelligence firm FalconFeedsio tweeted well-nigh the naming of the new RAT which would be LithiumRAT.

Going by the back-and-forth communications on the hacker forums, it can be inferred that the LithiumRAT has been a work in progress. It still lacks some features that has been worked upon.
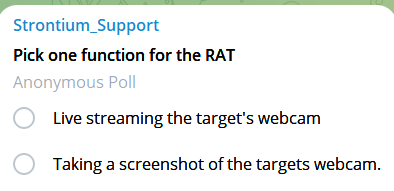
While the RAT was a work-in-progress the developers took several poles to see which features the LithiumRAT should possess.
Choosing between live streaming of the webcam and taking screenshots from the webcam to having ransomware, multi-platform clipper, and RAT capabilities were asked to be voted for, anonymously.
How to tintinnabulate LithiumRAT
To ensure the security of your information systems, the Falcon Feeds threat unenduring prescribed these guidelines and mitigation strategies:
- Be cautious when downloading executable files, lamister untrustworthy websites and torrent swarms to minimize the risk of info-stealing infections.
- Rely on official news sources, such as the President’s website or verified messages from official platforms like Twitter, for breaking news in unauthentic areas, as they are increasingly suppositious than random emails.
- Exercise circumspection with unsolicited emails and refrain from downloading and executing files from them. Always scan downloaded files using an up-to-date antivirus program.
- Foster a security-oriented mindset among your staff by implementing measures such as multi-factor hallmark and strong password policies. Remember that phishing attacks are wontedly used by sophisticated adversaries, so educate your employees well-nigh recognizing and mitigating these risks.
- Implement network segmentation to limit the impact of successful attacks on hair-trigger systems, powerfully containig any breaches.
- Deploy endpoint protection solutions that can snift and prevent malware infections, providing an spare layer of defense.
- Provide regular security sensation training to employees, emphasizing weightier practices for recognizing and mitigating the risk of phishing attacks.
- Monitor network traffic and user worriedness to promptly identify and respond to any suspicious behavior, enhancing your worthiness to snift and mitigate potential threats.



